docker-compose方式安装elasticsearch,并配置tls
官方文档链接
Setting Up TLS on a Cluster
Encrypting Communications in an Elasticsearch Docker Container
首先使用docker-compose安装elasticsearch,kibana
环境准备
创建一个空目录elk,创建以下4个文件:
instances.yml
instances:
- name: es01
dns:
- es01 //Allow use of embedded Docker DNS server names.
- localhost
ip:
- 127.0.0.1
- name: es02
dns:
- es02
- localhost
ip:
- 127.0.0.1
.env
CERTS_DIR=/usr/share/elasticsearch/config/certificates
ELASTIC_PASSWORD=xianfengmc
CERTS_DIR:在docker容器内部,证书的放置目录
ELASTIC_PASSWORD:内置用户elastic的密码
create-certs.yml:
version: '2.2'
services:
create_certs:
container_name: create_certs
image: ah4a.com/hub/elasticsearch:6.3.0
command: >
bash -c '
if [[ ! -d config/certificates/certs ]]; then
mkdir config/certificates/certs;
fi;
if [[ ! -f /local/certs/bundle.zip ]]; then
bin/elasticsearch-certgen --silent --in config/certificates/instances.yml --out config/certificates/certs/bundle.zip;
unzip config/certificates/certs/bundle.zip -d config/certificates/certs;
fi;
chgrp -R 0 config/certificates/certs
'
working_dir: /usr/share/elasticsearch
volumes: ['.:/usr/share/elasticsearch/config/certificates']
证书和CA证书及秘钥存储在当前目录的certs,其实这个文件就是为了创建试用自签名CA证书的,如果有了自己的CA证书,完全可以使用自己的证书。
因此本文不再使用此方法创建证书,而是使用我在Let's encrypt上申请的泛域名证书。首先下载申请的证书到certs目录,文件列表如下:
aiuyo.com.cer
aiuyo.com.conf
aiuyo.com.csr
aiuyo.com.csr.conf
aiuyo.com.key
ca.cer
fullchain.cer
这里证书为fullchain.cer,秘钥为:aiuyo.com.key,以下配置docker-compose.yml会用到
docker-compose.yml
version: '2.2'
services:
es01:
container_name: es01
image: docker.elastic.co/elasticsearch/elasticsearch:6.3.2
environment:
- node.name=es01
- discovery.zen.minimum_master_nodes=2
- ELASTIC_PASSWORD=$ELASTIC_PASSWORD
- "ES_JAVA_OPTS=-Xms512m -Xmx512m"
- bootstrap.memory_lock=false
- bootstrap.system_call_filter=false
- xpack.license.self_generated.type=trial
- xpack.security.enabled=true
- xpack.security.http.ssl.enabled=true
- xpack.security.transport.ssl.enabled=true
- xpack.security.transport.ssl.verification_mode=certificate
- xpack.ssl.certificate_authorities=$CERTS_DIR/fullchain.cer
- xpack.ssl.certificate=$CERTS_DIR/fullchain.cer
- xpack.ssl.key=$CERTS_DIR/aiuyo.com.key
volumes: ['esdata_01:/usr/share/elasticsearch/data', './certs:$CERTS_DIR']
ports:
- 9200:9200
healthcheck:
test: curl --cacert $CERTS_DIR/fullchain.cer -s https://localhost:9200 >/dev/null; if [[ $$? == 52 ]]; then echo 0; else echo 1; fi
interval: 30s
timeout: 10s
retries: 5
es02:
container_name: es02
image: docker.elastic.co/elasticsearch/elasticsearch:6.3.2
environment:
- node.name=es02
- discovery.zen.minimum_master_nodes=2
- ELASTIC_PASSWORD=$ELASTIC_PASSWORD
- discovery.zen.ping.unicast.hosts=es01
- "ES_JAVA_OPTS=-Xms512m -Xmx512m"
- bootstrap.memory_lock=false
- bootstrap.system_call_filter=false
- xpack.license.self_generated.type=trial
- xpack.security.enabled=true
- xpack.security.http.ssl.enabled=true
- xpack.security.transport.ssl.enabled=true
- xpack.security.transport.ssl.verification_mode=certificate
- xpack.ssl.certificate_authorities=$CERTS_DIR/fullchain.cer
- xpack.ssl.certificate=$CERTS_DIR/fullchain.cer
- xpack.ssl.key=$CERTS_DIR/aiuyo.com.key
volumes: ['esdata_02:/usr/share/elasticsearch/data', './certs:$CERTS_DIR']
wait_until_ready:
image: docker.elastic.co/elasticsearch/elasticsearch:6.3.2
command: /usr/bin/true
depends_on: {"es01": {"condition": "service_healthy"}}
volumes: {"esdata_01": {"driver": "local"}, "esdata_02": {"driver": "local"}}
解释一下:
ELASTIC_PASSWORD:使用了.env中定义的引导密码。点击以下链接,查看引导密码的详情The Elastic bootstrap password
xpack.license.self_generated.type:为了启用x-pack的安全功能,默认申请了一个试用版的订阅
xpack.security.transport.ssl.verification_mode:certificate 证书模式
docker-compose方式启动elasticsearch
切换到docker-compose.yml文件所在目录,使用如下命令启动elasticsearch
docker-compose up -d
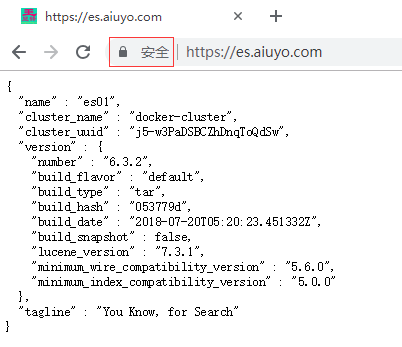
启动之后就可以通过https的方式访问了,一开始进入页面的时候需要需要用户elastic和上面定义的密码(这里是xianfengmc),访问成功页面在chrome中显示如下:
安装kibana,添加到docker-compose当中
这里首先把kibana加入到了docker-compose.yml文件当中,作为服务启动,然后在kibana.yml文件中进行配置kibana。
官方文档
Encrypting communications in Kibana
把kibana加入到docker-compose
在以上docker-compose.yml文件的wait_until_ready之前添加以下内容,注意缩进:
kibana:
image: docker.elastic.co/kibana/kibana:6.3.2
environment:
SERVER_NAME: kb.aiuyo.com
ports:
- 5601:5601
volumes:
- ./certs:/usr/share/kibana/config
- ./kibana.yml:/usr/share/kibana/config/kibana.yml
- ./hosts:/etc/hosts
解释一下:
1. kibana镜像使用docker.elastic.co/kibana/kibana:6.3.2版本
2. SERVER_NAME使用kb.aiuyo.com,和es使用相同的一级域名aiuyo.com,不同的二级域名。
3. kibana端口使用5601
4. 把certs目录下的所有文件挂载到/usr/share/kibana/config,以便在kibana.yml中进行配置
5. 把配置文件放在当前目录下的kibana.yml,挂载到容器中对应的位置/usr/share/kibana/config/kibana.yml
6. 重写容器的/etc/hosts文件,是为了能够自定义解析域名
kibana.yml配置
kibana的配置全部放入kibana.yml文件中:
server.name: kibana
server.host: "0"
elasticsearch.url: "https://es.aiuyo.com:443"
xpack.monitoring.ui.container.elasticsearch.enabled: true
xpack.security.enabled: true
elasticsearch.username: "elastic"
elasticsearch.password: "xianfengmc"
xpack.security.encryptionKey: "d5038994822d03bf1352049337b740e1e05682c071963a98"
xpack.security.sessionTimeout: 60000000
server.ssl.enabled: true
server.ssl.certificate: /usr/share/kibana/config/fullchain.cer
server.ssl.key: /usr/share/kibana/config/aiuyo.com.key
elasticsearch.ssl.certificate: /usr/share/kibana/config/fullchain.cer
elasticsearch.ssl.key: /usr/share/kibana/config/aiuyo.com.key
elasticsearch.ssl.verificationMode: "certificate"
解释一下:
1. server.name:自定义服务名,随便定义,默认kibana
2. server.host:服务主机地址,这里默认定义为0,没啥事不要修改,否则起不来
3. elasticsearch.url:ES的地址,这里定义为https://es.aiuyo.com:443,需要指定端口,否则默认连接9200端口
4. xpack.monitoring.ui.container.elasticsearch.enabled:是否开启监控,这里配置为true
5. xpack.security.enabled: true
elasticsearch.username: "elastic"
elasticsearch.password: "xianfengmc"
这3个参数配置ES的x-pack安全设置,意思是启用x-pack安全,并输入用户名和密码
6. xpack.security.encryptionKey:这个是官方定义的x-pack加密密码,任意的大于等于32位的字符串
7. xpack.security.sessionTimeout:前台会话超时时间
8. server.ssl.enabled: true
server.ssl.certificate: /usr/share/kibana/config/fullchain.cer
server.ssl.key: /usr/share/kibana/config/aiuyo.com.key
这3个参数是启用kibana自身的tls,并配置证书。
9. elasticsearch.ssl.certificate: /usr/share/kibana/config/fullchain.cer
elasticsearch.ssl.key: /usr/share/kibana/config/aiuyo.com.key
elasticsearch.ssl.verificationMode: "certificate"
这3个参数是连接ES所需要的配置,包括证书和认证方式
集成了elasticsearch、kibana的docker-compose.yml文件
version: '2.2'
services:
es01:
container_name: es01
image: docker.elastic.co/elasticsearch/elasticsearch:6.3.2
environment:
- node.name=es01
- discovery.zen.minimum_master_nodes=2
- ELASTIC_PASSWORD=$ELASTIC_PASSWORD
- "ES_JAVA_OPTS=-Xms512m -Xmx512m"
- bootstrap.memory_lock=false
- bootstrap.system_call_filter=false
- xpack.license.self_generated.type=trial
- xpack.security.enabled=true
- xpack.security.http.ssl.enabled=true
- xpack.security.transport.ssl.enabled=true
- xpack.security.transport.ssl.verification_mode=certificate
- xpack.ssl.certificate_authorities=$CERTS_DIR/fullchain.cer
- xpack.ssl.certificate=$CERTS_DIR/fullchain.cer
- xpack.ssl.key=$CERTS_DIR/aiuyo.com.key
volumes: ['esdata_01:/usr/share/elasticsearch/data', './certs:$CERTS_DIR']
ports:
- 9200:9200
healthcheck:
test: curl --cacert $CERTS_DIR/fullchain.cer -s https://localhost:9200 >/dev/null; if [[ $$? == 52 ]]; then echo 0; else echo 1; fi
interval: 30s
timeout: 10s
retries: 5
es02:
container_name: es02
image: docker.elastic.co/elasticsearch/elasticsearch:6.3.2
environment:
- node.name=es02
- discovery.zen.minimum_master_nodes=2
- ELASTIC_PASSWORD=$ELASTIC_PASSWORD
- discovery.zen.ping.unicast.hosts=es01
- "ES_JAVA_OPTS=-Xms512m -Xmx512m"
- bootstrap.memory_lock=false
- bootstrap.system_call_filter=false
- xpack.license.self_generated.type=trial
- xpack.security.enabled=true
- xpack.security.http.ssl.enabled=true
- xpack.security.transport.ssl.enabled=true
- xpack.security.transport.ssl.verification_mode=certificate
- xpack.ssl.certificate_authorities=$CERTS_DIR/fullchain.cer
- xpack.ssl.certificate=$CERTS_DIR/fullchain.cer
- xpack.ssl.key=$CERTS_DIR/aiuyo.com.key
volumes: ['esdata_02:/usr/share/elasticsearch/data', './certs:$CERTS_DIR']
kibana:
image: docker.elastic.co/kibana/kibana:6.3.2
environment:
SERVER_NAME: kb.aiuyo.com
ports:
- 5601:5601
volumes:
- ./certs:/usr/share/kibana/config
- ./kibana.yml:/usr/share/kibana/config/kibana.yml
#- ./hosts:/etc/hosts
wait_until_ready:
image: docker.elastic.co/elasticsearch/elasticsearch:6.3.2
command: /usr/bin/true
depends_on: {"es01": {"condition": "service_healthy"}}
volumes: {"esdata_01": {"driver": "local"}, "esdata_02": {"driver": "local"}}
成功显示kibana的页面:

filebeat发送日志给ES tls配置
这部分比较简单,只是在配置filebeat的ES输出的时候添加证书的配置即可。
#-------------------------- Elasticsearch output ------------------------------
output.elasticsearch:
# Array of hosts to connect to.
hosts: ["https://es.aiuyo.com:443"]
username: "elastic"
password: "xianfengmc"
ssl.certificate: "/fullchain.cer"
ssl.key: "/aiuyo.com.key"
只是注意需要把证书挂载到容器当中,路径配置对即可。
常见问题
- 期间也遇到了像上次安装一样的问题,按照上次的方法解决了docker安装elasticsearch,elasticsearch集群和kibana
- 这次遇到了一个新的问题,就是docker容器中uid和gid都是1000,如果宿主机中的1000用户对挂载的文件没有访问权限,那么在容器当中就会报错。由于DSM没有usermod命令,本次是通过直接修改/etc/passwd中的uid解决的,不知道会不会有什么后遗症,先不管了。
内网穿透术
为什么我没有按照配置文件中的端口进行访问,比如9200,5601端口,因为我使用了内网穿透术,详情参考nginx反向代理frp缓存加速http+https。
传统方式与docker安装的不同之处
传统方式安装不同之处在于直接修改配置文件,而docker安装可以通过设置环境变量,当然也可以直接修改配置文件进行挂载。
由于elastic官方封装docker的时候设置了ELASTIC_PASSWORD的密码,可以通过环境变量设置内置用户的密码,但是直接安装没有这个配置项,通过查看官方的docker封装脚本,可以看出直接安装需要通过以下方式设置内置用户的密码:
cd ~/elasticsearch/bin
./elasticsearch-keystore add -x 'bootstrap.password'
这时候需要输入想要设置的密码,输入完成之后设置成功。
文章评论